Scholarship recipients have been announced !
Follow us on LinkedIn for more details on the official announcement.
The new Executive Master in Cybersecurity Management (EMCM) restarted in March 2023 after two years of interruption due to the Pandemic. With a new hybrid education method and an evolved curriculum, the programme is available for registration to senior participants in the whole of Europe.
Solvay Lifelong Learning is, once again, offering in collaboration with Women4Cyber:
-
-
- One Full scholarship. The laureate gets a 100% waiver on her participation fee and administrative fees.
- Three half scholarships. The three laureates get a 50% waiver on their participation fee and the totality of administrative fees.
-
Who is the programme aimed at?
Profile
This programme is intended for professionals requiring managerial and practical knowledge of the six domains representing the pillars of cybersecurity activities and management practices.
Key admissions criteria
- At least 5 years as a digital or cybersecurity manager
- Actively involved in digital or cybersecurity activities and decision-making.
Full Scholarship recipient from the past edition
My expectations were high. I knew already that it would be something advanced but it took me by surprise how great it is to be among these top level cyber managers and experts. You get to meet a lot of people who work in the field that otherwise you wouldn’t. I get to spend time with the best of the best in the cyber world and learn a lot. Definitely worth applying for the programme. I managed to do it from Montenegro so everything is possible!
Overview of the programme
This programme is intended for professionals requiring managerial and practical knowledge of the six domains representing the pillars of cybersecurity activities and management practices.
A combination of 6 bodies of knowledge
1. Information Security Leadership
January – February 2024
The core management activities of a modern information security leader includes the security governance process, the risk management process, the program management process and the incident management process. This module will cover the job description of a typical CISO today and where the CISO fits within the organisation including reporting lines and responsibilities, skills and expertise; talk about the typical challenges CISO’s face in their role
4. Security Operations
September – October 2024
This module will build upon the concepts of the previous modules where Information Security Governance, the Implementation of Security Controls, implementing a Secure Architecture are key building blocks to set up a qualitative Security Operations team.
2. Security Controls
March – April 2024
This module will take participants through the process of analysing context, defining scope, modelling threats, defining security controls and requirements, considering the solution space for controls, including technologies and operating models, and then finally evaluating risk (Inherent vs. Residual) and anchoring in policy, providing assurance that the controls operate as intended, e.g., for the purpose of internal or external assurance obligations or certification. This part builds on concepts introduced in module 1
(Information Security Leadership).
5. Cybersecurity Battleground
November – December 2024
Cybersecurity management practices require the knowledge of own business, its functional and technical vulnerabilities and the threat landscape that needs to be addressed. The capabilities that require building cybersecurity capacity includes Identification, Protection, Detection, Response and Recovery techniques and processes.
3. Security Architecture
May – June 2024
Often people talk about “security-by-design” or “privacy-by-design”. Indeed, security cannot be “bolted on” at a later stage effectively. The better security is embedded “by design” in all layers of your organization’s business, enterprise, and
solution architecture and the better it is embedded in your design/delivery as well as run and operations, the better you will be able to understand your security posture and outstanding gaps and risks.
6. General Management
Spread over the year
This module will take participants through the basics of General Management dedicated to Cybersecurity and Digital professionals. There will be four parts: Finance, Strategy, Leadership and Human Capital. In the first part, participants will better understand the art and the language of finance. The topics that should be reviewed are the challenges of the income statement, the balance
sheet, cash, financial ratios, return on investment and working capital.
More programme feautures
Blended and Hybrid education model
The first five modules are delivered in two months each with a combination of self-paced and ex-cathedra class on-site (also available in virtual/online format for those unable to attend physically). Blended Learning is applied for each module as follows:
Part 1 (Acquire in an offline learning mode): Plan for a minimum of 12 hours of self-learning where participants obtain self-study resources.
Part 2 (Evaluate): Short self evaluation survey before attending on-site classes.
Part 3 (Build expertise): Attend onsite classes and workshops that are also available remotely.
Part 4 (Group Case study): Work in groups on a business case addressing specific cases related to each module.
Part 5 (Final delivery): Participants present their business cases to a jury and pass a knowledge-based exam.
Adjusted to your own needs and career targets
A career development tool is available to participants to assess their competences against current or targeted roles.
On that basis, they adjust their education experience to focus on those domains that they require most.
As a result, both phases 1 (Acquire) and 4 (Case study) are required to address those focus areas.
A personal acceptance interview is conducted to formalise the study plan and to level up the participants.
An exit interview is conducted at the graduation time.
SELECTION CRITERIA FOR THE SCHOLARSHIPS
Participants must meet the key admission criteria:
-
- At least 5 years as a digital or cybersecurity manager
- Actively involved in digital or cybersecurity activities and decision-making
Participants must be able to follow the programme if accepted
The recipients of the scholarship will be selected based on:
-
- Motivation
- Capacity
- Impact
- Availability
- Values
This will be assessed through their application form
APPLICATION PROCESS
All participants must apply for the scholarship through the form below
Applications close on August 15, 2023 at 23:00 CET.
The Jury will evaluate the applications based on the criteria stated above.
Scholarship recipients will be announced on September 11, 2023.
TIMELINE
- June 28, 2023: Scholarship application open
- Aug 15, 2023: Deadline for applications 23:00 CET
- Sep 11, 2023: Announcement of the winners of the scholarship
- Sep 15 – Oct 15: Additional enrolment steps
- Jan 08, 2024: Start of the programme
- April: Award ceremony at CyberSec Europe (TBC)
JURY

Karin Doguet
SBS-EM
CEO, Solvay Lifelong Learning; Credendo Guarantees & Special Risks, External Independent Director; Membre du Comité de Gestion

Georges Ataya
SBS-EM
Professor at Solvay Brussels School and Vice-President of the Cybersecurity Coalition
Academic Director

Frédéric Roos
SBS-EM
Academic Programme Manager
Academic Director

Sanja Kekic
W4C Serbia
Women4Cyber Serbia President
Immediatie Past President ISACA Belgrade Chapter

Liga Rozentale
Līga Rozentāle Consulting
Managing Director/Consultant
ENISA Advisory Group 2023-2025, reserve expert 2020-2023

Ana Ferreira
Healthcare Security and Privacy Senior Researcher – CINTESIS@RISE/FMUP | Member of ENISA AG | EU Top100 Women in Cyber | Mentor | Women4Cyber PT Co-Founder | PT (ISC)2 Chapter Co-Founder
Curiosities about Solvay Business School
Solvay Business School was created in 1903 (120 years ago) and in 1927 it hosted the legendary meeting with one the first prestigious women in tech among all other scientists, Marie Curie.
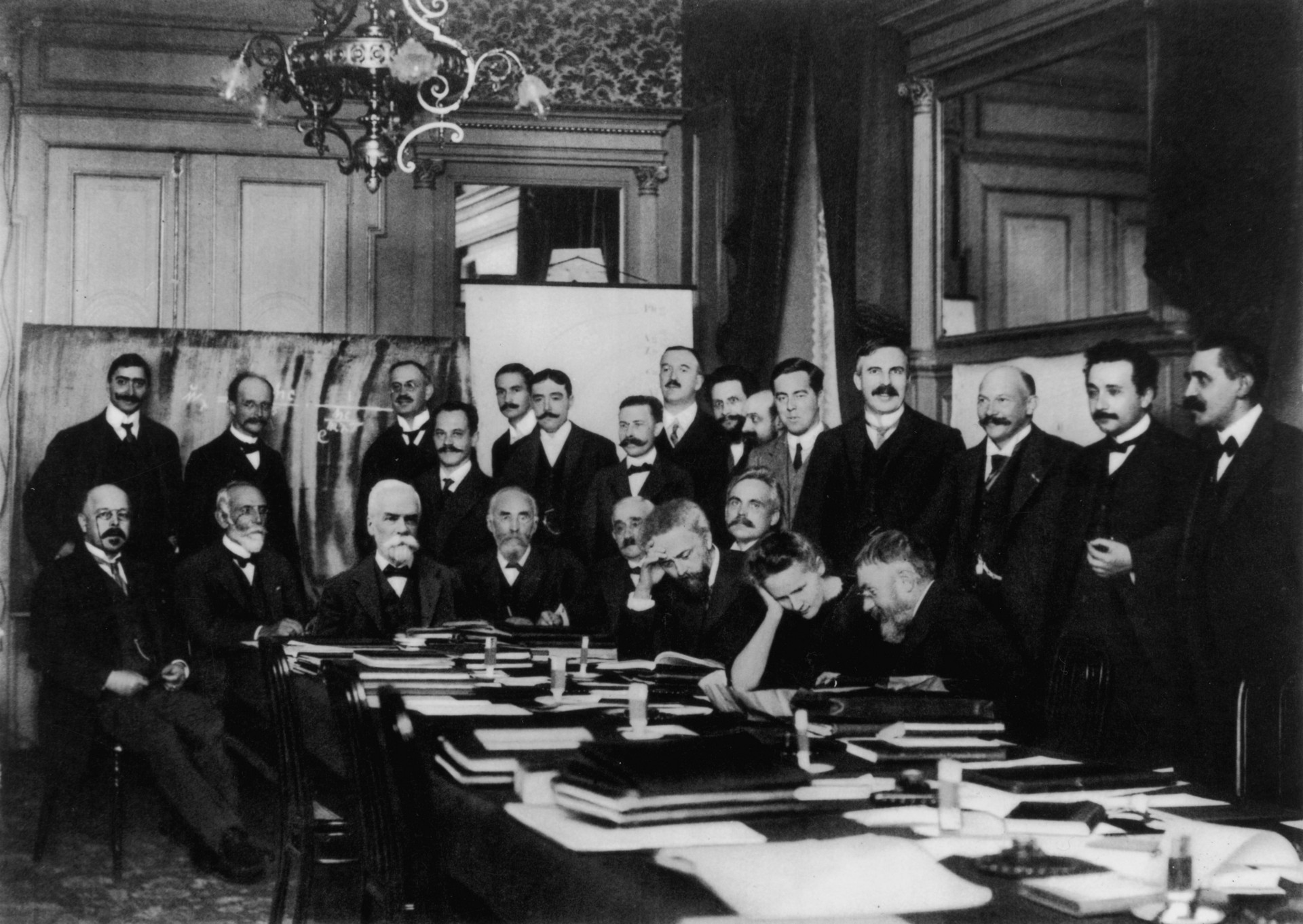
First Solvay Conference (1911), Curie (seated, second from right) confers with Henri Poincaré; standing, fourth from right, is Rutherford; second from right, Einstein; far right, Paul Langevin

“1927 SOLVAY CONGRESS in Brussels bringing together atomic theoreticians”. In the front row, Max Planck was second from left next to Marie Curie, Albert Einstein fifth in the second row, and Nils Bohr at far right.

Sponsoring Partners